Instagram has become the bellwether of all the social media platforms recently and has been reputed as the best forum to share stories and photos. Snippets of your life to any events are shared via this platform and people across the world use this in abundance without any inhibitions. Even the so-called celebrities to well-known personalities are recipients of this social media platform and their accounts are being watched and followed incessantly.
Instagram is also considered as age-agnostic as people of any age can register themselves in the application without any filter. This behoves the parents to keep an eye on the children who are more digital-bound these days and their proximity to access anything unwanted or beyond age compels a validation on what they browse. However, Instagram as an application has made all efforts to conceal its content and does not allow any external invasion to bits.
This property of Instagram has propelled the users to consume it relentlessly as they have high regard for its security aspects. However, spying software has been on the rise and the one known as SpyMyfone has been quite helpful in hacking any Instagram account without alarming the person who owns it.
Features and functionality of SpyMyfone:
- This is hacking software that does not restrict its functionality only to Instagram, but also be used for tracking SMS, phone logs, etc.
- Using this application evades you from any kind of inspection or suspicion from anyone who is accessing the same account.
- If you catch sight of any direct messages on the platform, you can directly take a screenshot and record it without leaving any shred of evidence.
- It is also used for geo-tracking purposes, along with fencing, messaging, and tracking every detail of your intruding device.
- This is also device-friendly as it adapts to iOS as much as it does to any Android device, be it a phone or a system irrespectively.
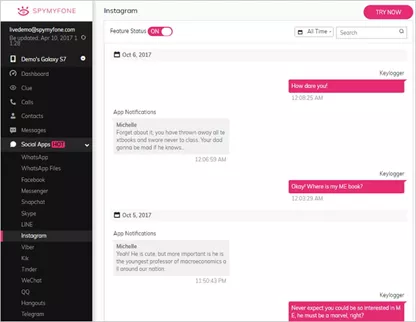
- The keylogger feature of the app records the credentials when it is applied on the application via keyboard.
Steps to implement hacking:
As mentioned earlier, it is compatible with any device, be it Android or iOS. However, the steps each of them entails will differ according to the protocols of what you own. Let us follow the below procedure intact to accomplish hacking adequately.
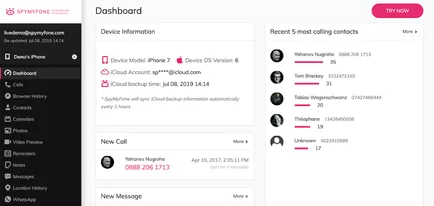
- Sign up for the SpyMyfone application by filling in the essential details. You need to register for the app, which could either be a demo account or a properly paid bot account. An email will be sent as an approval or confirmation of owning an account. The link will be attached in the mail, which can be availed to install the application on your device.
- If you own an Android device, all you have to do is install the application in your intruded device by filling out all the essential information about the owner of the website. If it is an iOS device, iCloud details of the target account need to be registered without fail.
- Select the appropriate device of your target account as to whether it is iOS or Android.
- After all the installation on the intruded device is complete in either of the device platforms, you can go ahead logging into your SpyMyfone account to sneak access into the target account.
The above are the methods you follow thoroughly to track and hack the Instagram account. As mentioned earlier, this application extends its features to SMS and phone logs, where the procedure emulates the above-mentioned steps approximately.
Let us quickly look into the horizons it expands its access to and what are areas it covers when it comes to tracking.
Before we swirl our way into its expansion, let us also get to know some of its additional benefits which provoke people to buy the app immediately.
Benefits of the application in short:
- 5 minutes of set up time suffices to use it effectively.
- 100% invisibility is guaranteed even in any adverse scenario.
- Information keeps piling up into your system within 5 minutes of any new updates.
- Data is stored and protected without a hint of any external invasion.
- It is not very expensive and most affordable to everyone without any limitations.
As mentioned earlier, its functionalities extend to
Calls: incoming and outgoing calls along with minute timestamp details and caller information.
GPS: Current location to location visited is tracked and stored without any glitch.
Browser History: Browser history, again with minute details of tracking including time and time spent with bookmarks that were browsed.
Messengers: All chat application is within its territory – WhatsApp, Snapchat, Skype, Telegram, Viber, and Hangout, etc.
Social media platforms: Facebook, Instagram, Twitter, and Tinder, etc.
Photos and media: All media files which include the information about its downloading, uploading, viewing, saving, sharing, and receiving are all tracked and stored exquisitely.
The other applications include phone logs, which again cover all the information regarding your phone calls and contacts you have accessed is recorded. Emails installed applications, and Wi-Fi networks are also easily pierceable by the application without much of ado.
Conclusion:
Hacking has been a heinous crime ever since the advent of technology changed our lives massively. However, hacking and spying when it is needed to keep track deem important in this unfiltered world which is beaming with digital apps all over. The only thing we need to be wary of is the protocols that need to be followed when we embark on a mission like this. As security and safety of our data precede the benefit of using any advanced technology that prevails or is on the rise across the world.